About Ransomware
Ransomware malware viruses infect a computer and make the user’s files inaccessible by encrypting them. In some cases the computer is left only partially usable. The user is given some instructions on how to get their files back. Usually this involves communicating directly with someone who will ask you for money before they will let you have access to your files again. They may also promise to fix the computer so that it will function again.
It is estimated that there are presently over 250,000 kinds of ransomware viruses. In 2013, just one of these viruses alone resulted in the extortion of an accumulated $3 million from all its victims before it was taken down by authorities. (source)
Ransomware Prevention
Some antivirus software providers, such as Kaspersky, promise that their software can protect against ransomware. This statement is on the Kaspersky website:
“To protect your computer from ransom malware, download and install Kaspersky Internet Security 2015. The application provides high-level protection against ransom malware.” (source)
Avoid Pop-Up Messages. Another important prevention measure is to be very careful with any unusual pop-up messages. Avoid clicking until you can be certain that the message is legitimate, or simply shut down the computer and restart.
Take Email Precautions. One way of getting ransomware is clicking on links in spam emails. Services like Gmail from Google examine all emails flowing through their system and monitor for malicious activity. So, for example, let’s say there is a fake message claiming to be from FedEx about a package that couldn’t be delivered. Google would likely identify that email as not having authentically been sent from Federal Express. So, it would end up in your spam folder with a notice, “We couldn’t verify that this message was really from the claimed sender” or “We’ve identified other messages like this one that are malicious.”
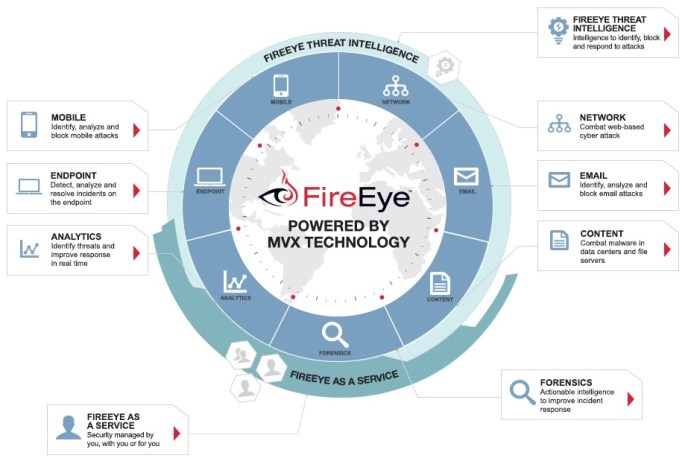
Use AntiVirus Software. Most antivirus software should prevent virus-like activity even from viruses that were previously unknown. Comprehensive Antivirus software can warn you of known malicious websites. In this way, they make browsing the web safer.
Use an Apple Computer. There are currently over 17 million known Windows computer viruses. The current number of Apple viruses are currently very limited. Apple computers are susceptible to security problems found in Adobe Flash and Java, so it’s important to stay updated. There have been a few fake Apple programs people have been deceived into installing, such as Mac Defender. A report of Apple viruses over the past 10 years is only a few pages long. (source) So, while Apple computers are not completely immune to viruses, they may be a better choice for security minded people.
Ransomware Protection
As described above, there are some preventative measures you can take. Ransomware protection are measures you can take to protect and limit the potential damage of a Ransomware attack.
Backups. Some backup programs run daily to maintain a backup of all your files. This is helpful, except in cases where your files have become corrupted or maliciously encrypted. In some cases, a good backup can be overwritten by a bad one. Also, a connected backup drive is accessible to viruses that might try to erase or encrypt files. In these cases, it may be best to maintain a separate manual backup of your files on a drive that remains disconnected from your computer in a safe place.
Cloud Synchronization. If you use a service like Dropbox to maintain a synchronized cloud copy of your files, make sure you have the ability to access previous versions of your files in the event they get damaged.
Ransomware Recovery
The most recent update about ransomware is an article from Sophos on 30 January 2015. (source) The article states:
Crypto-Ransomware is a family of malware that takes files on a PC or network storage, encrypts them, and then extorts money to unlock the files. … These encryptor malwares will encrypt pictures, documents, and videos, and then leave a ransom note in each directory after encrypting at least one file in that directory. They also typically attempt to do this to mapped network drives [or attached backup drives] as well. … Ransomware-encrypted files for most variants cannot be recovered at all. The encryption keys are not stored on the system. There is one variant which can be recovered, which is discussed below. … W32/VirRnsm-A infects files and changes them to .exe files, including the virus code. It still allows the file to open initially so it has a chance to spread. After a while it locks out the files. The good news is that these files, unlike most ransomware, can be recovered and cleaned by Sophos. A full system scan will fix and recover your files.” (source)
With so many variations of ransomware, it’s unlikely that encrypted files could be recovered unless they happen to be the result of the W32/VirRnsm-A variant.
Yet, some tools from Kaspersky (listed below) suggest that decryption may be possible if you have an original file that’s not encrypted and can compare this to an encrypted file.
Further Reading
Below are ransomware information pages from various sources.
Software Tools
Here are some software tools that might help with removal and/or recovery of files.
- Kaspersky WindowsUnlocker – The Kaspersky WindowsUnlocker utility is designed to disinfect registries of all operating systems installed on the computer (including operating systems installed on different partitions or in different folders on one partition) and disinfect user registry trees. Kaspersky WindowsUnlocker does not perform any actions with files (in order to disinfect files you can use Kaspersky Rescue Disk).
- RakhniDecryptor – utility for removing Trojan-Ransom.Win32.Rakhni
- RannohDecryptor – If the system is infected by a malicious program of the family Trojan-Ransom.Win32.Rannoh, Trojan-Ransom.Win32.AutoIt, Trojan-Ransom.Win32.Fury, or Trojan-Ransom.Win32.Cryakl, all files on the computer will be encrypted. To decrypt files affected by Trojan-Ransom.Win32.Rannoh, Trojan-Ransom.Win32.AutoIt, Trojan-Ransom.Win32.Fury, Trojan-Ransom.Win32.Crybola or Trojan-Ransom.Win32.Cryakl, use the RannohDecryptor utility.
- RectorDecryptor – Kaspersky Lab specialists have developed a special utility for decrypting the data encrypted by Trojan-Ransom.Win32.Rector. Cybercriminals use Trojan-Ransom.Win32.Rector for disrupting normal performance of computers and for unauthorized modification of data making it unusable. Once the data has been “taken hostage” (blocked), its owner (user) receives a ransom demand. The victim is supposed to deliver the ransom in exchange for pirate’s promise to send a utility that would restore the data or repair the PC.
- XoristDecryptor – There is a utility to confront malware of the family Trojan-Ransom.Win32.Xorist, Trojan-Ransom.MSIL.Vandev – XoristDecryptor. Malware of the family Trojan-Ransom.Win32.Xorist, Trojan-Ransom.MSIL.Vandev is designed for unauthorized modification of data on a victim computer. It makes computers uncontrollable or blocks its normal performance. After taking the data as a “hostage” (blocking it), a ransom is demanded from the user. The victim is supposed to deliver the ransom to the pirate, who is promising to send in return a program which would release the data or restore normal performance of the computer.
Instructional Videos
These videos refer to variants of ransomware. They may not be specific to your own experience, but the general information presented should be helpful. These videos provide an insight into the variety of ransomware and what the recovery solutions might be.
[youtube https://www.youtube.com/watch?v=_dKBXeoLIFo]
[youtube https://www.youtube.com/watch?v=w_7wUXzhRD8]
[youtube https://www.youtube.com/watch?v=WJagR2txHJU]
[youtube https://www.youtube.com/watch?v=LKy9X–ffw8]
[youtube https://www.youtube.com/watch?v=Zcj9RKO3e38]
41.661128
-91.530168